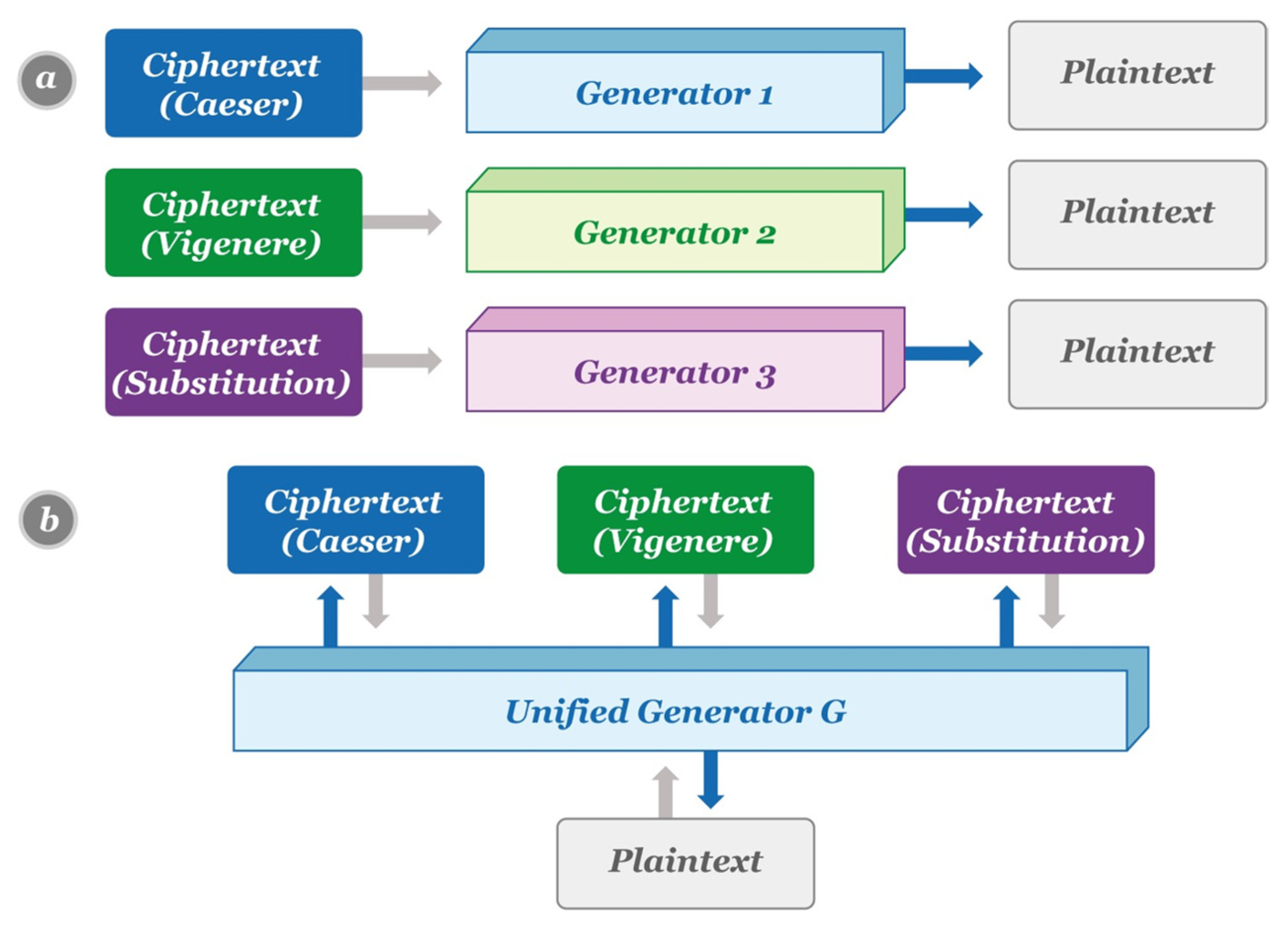
Cryptography | Free Full-Text | Automated Classical Cipher Emulation Attacks via Unified Unsupervised Generative Adversarial Networks
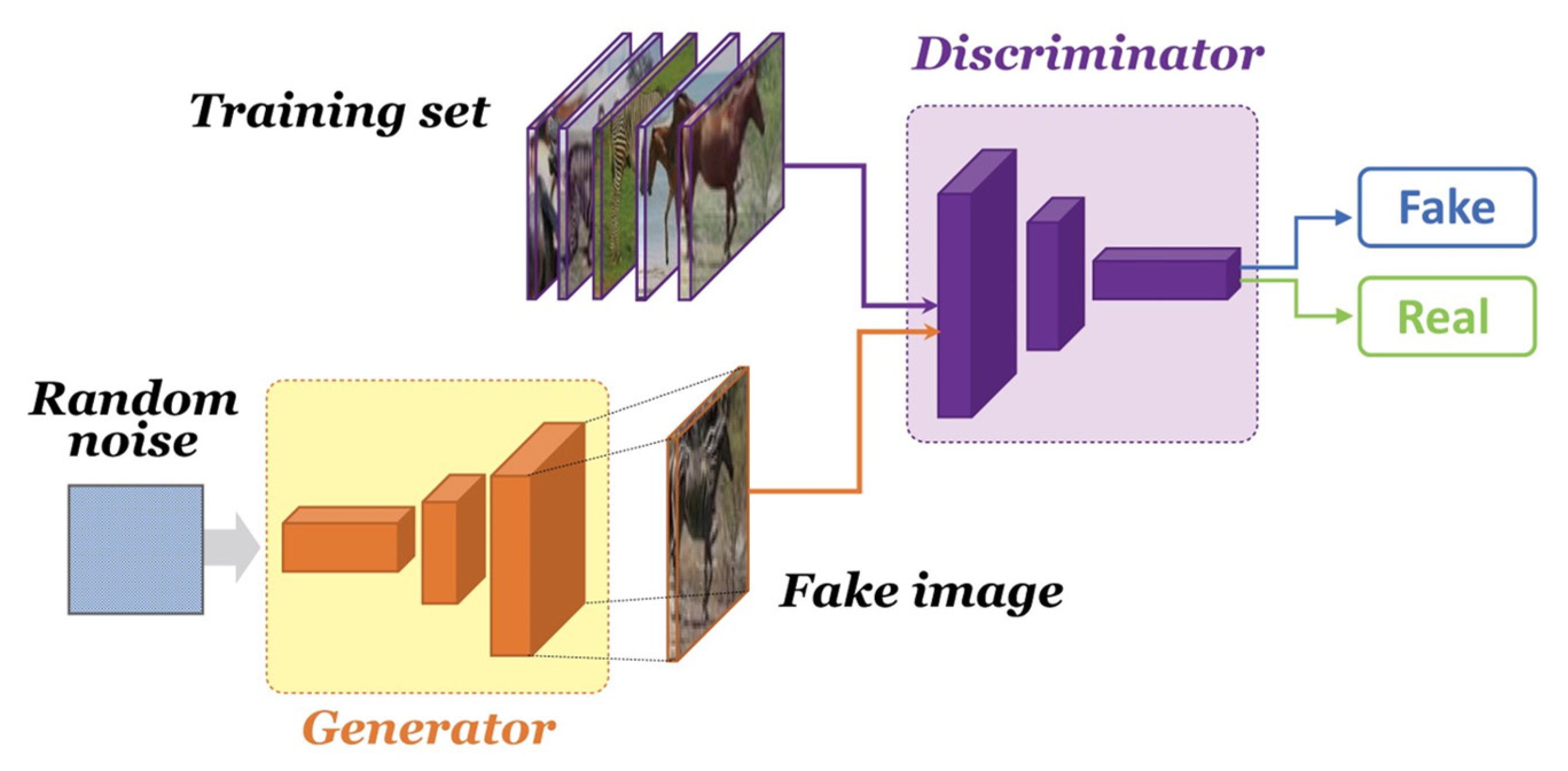
Cryptography | Free Full-Text | Automated Classical Cipher Emulation Attacks via Unified Unsupervised Generative Adversarial Networks

Hybrid Symmetric Cryptography: A System for Symmetric Key Cryptography using Dynamic Key & Linear Congruential Generator: Mehmood, Zeenat, Khan, Mohd Ilyas, Siddiqui, Abdul Moiz: 9783659483042: Amazon.com: Books

Pseudo-random permutation generators and cryptographic composition | Proceedings of the eighteenth annual ACM symposium on Theory of computing
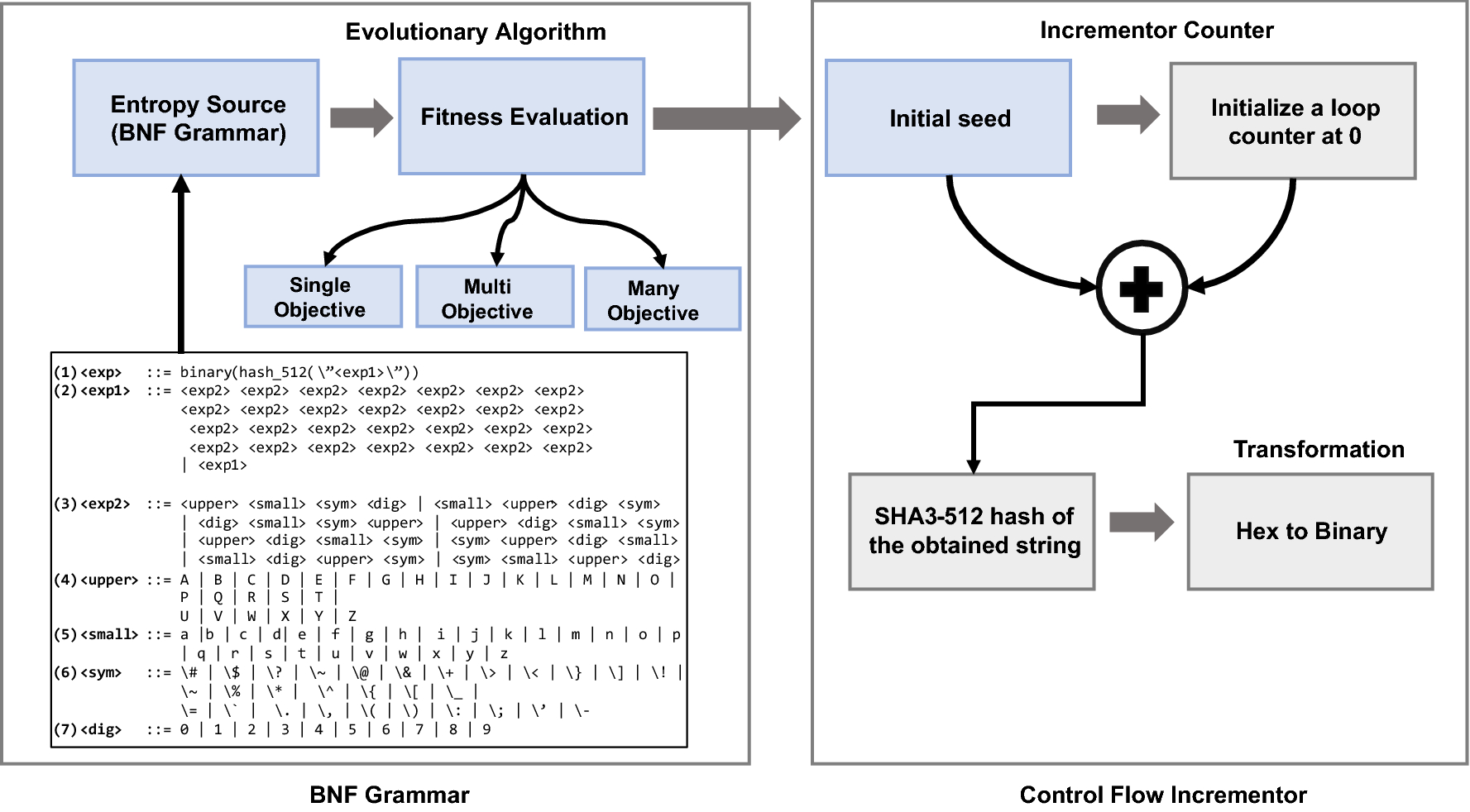
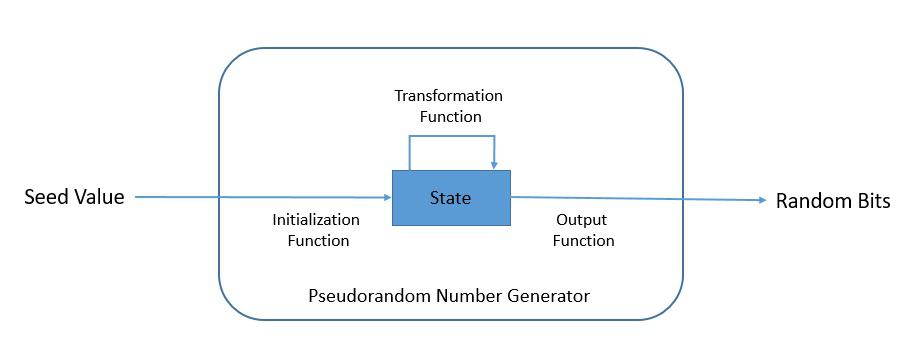
Design of a cryptographically secure pseudo random number generator with grammatical evolution | Scientific Reports
Automated cryptocode generator is helping secure the web | MIT News | Massachusetts Institute of Technology
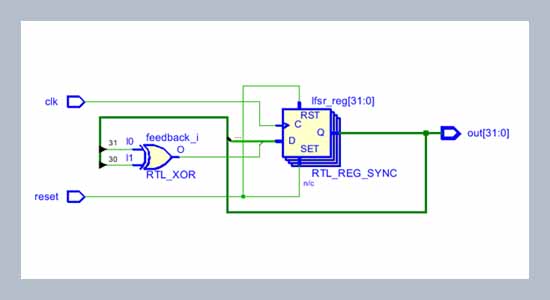
FPGA implementation of random number generator using LFSR and scrambling algorithm for lightweight cryptography
Example of key generation for code-based cryptography. The two matrixes... | Download Scientific Diagram





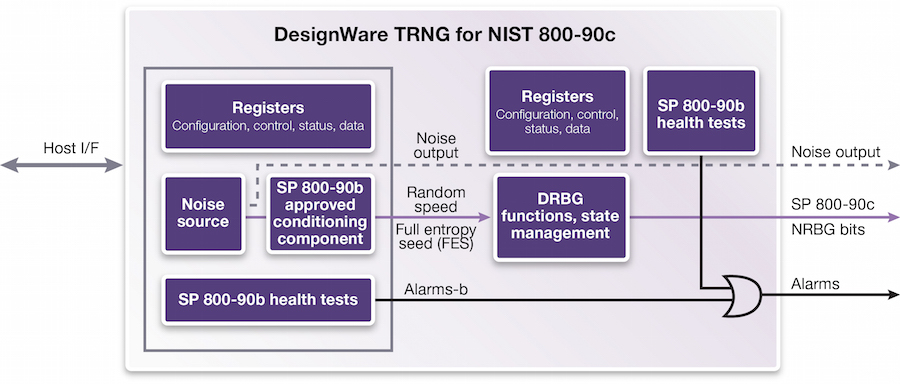
![PDF] Hardware Random number Generator for cryptography | Semantic Scholar PDF] Hardware Random number Generator for cryptography | Semantic Scholar](https://d3i71xaburhd42.cloudfront.net/d40db1ffcac69cd2bab55d7f50159922eaa2b5bf/2-Figure1-1.png)