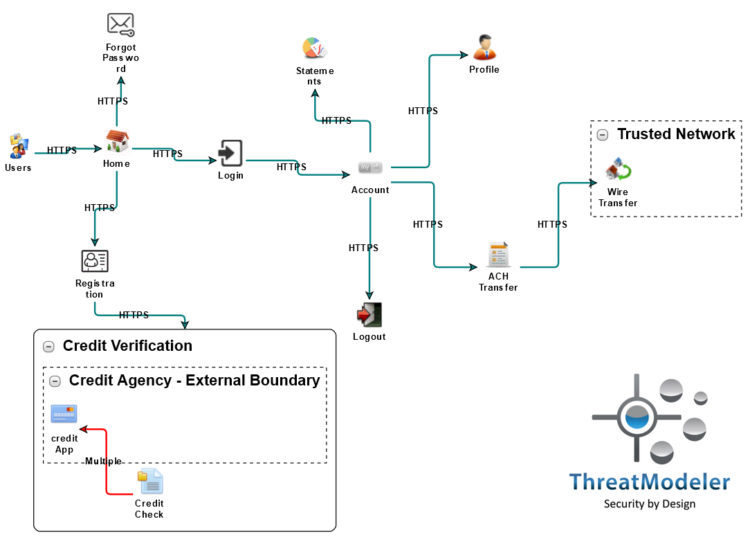
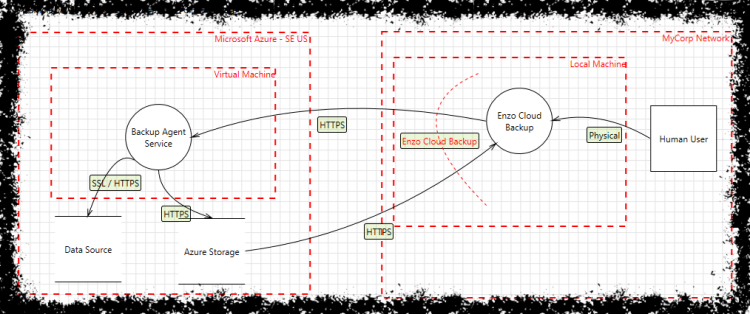
A Data Flow Diagram of CloudRAID showing Entry Points, Exit Points,... | Download Scientific Diagram
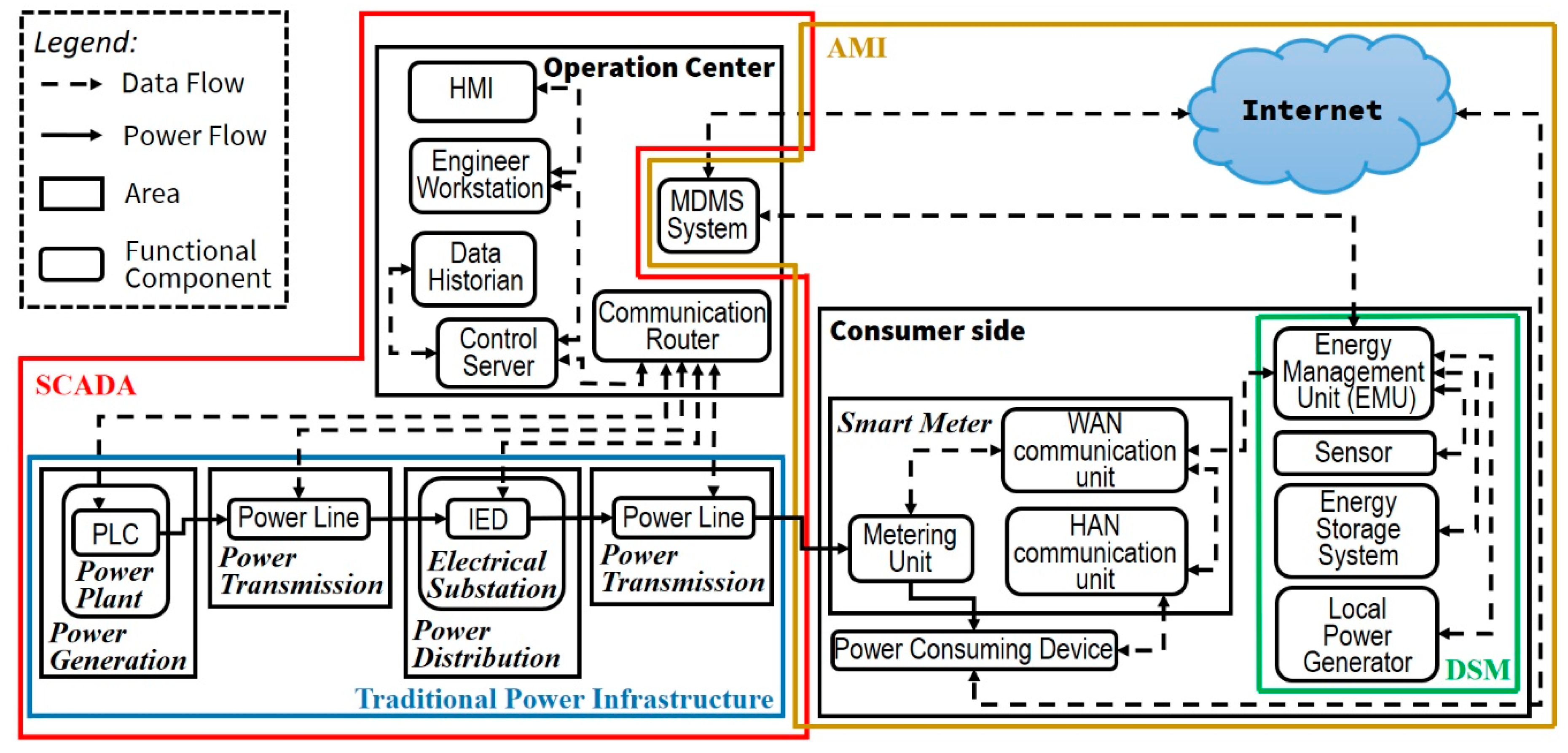
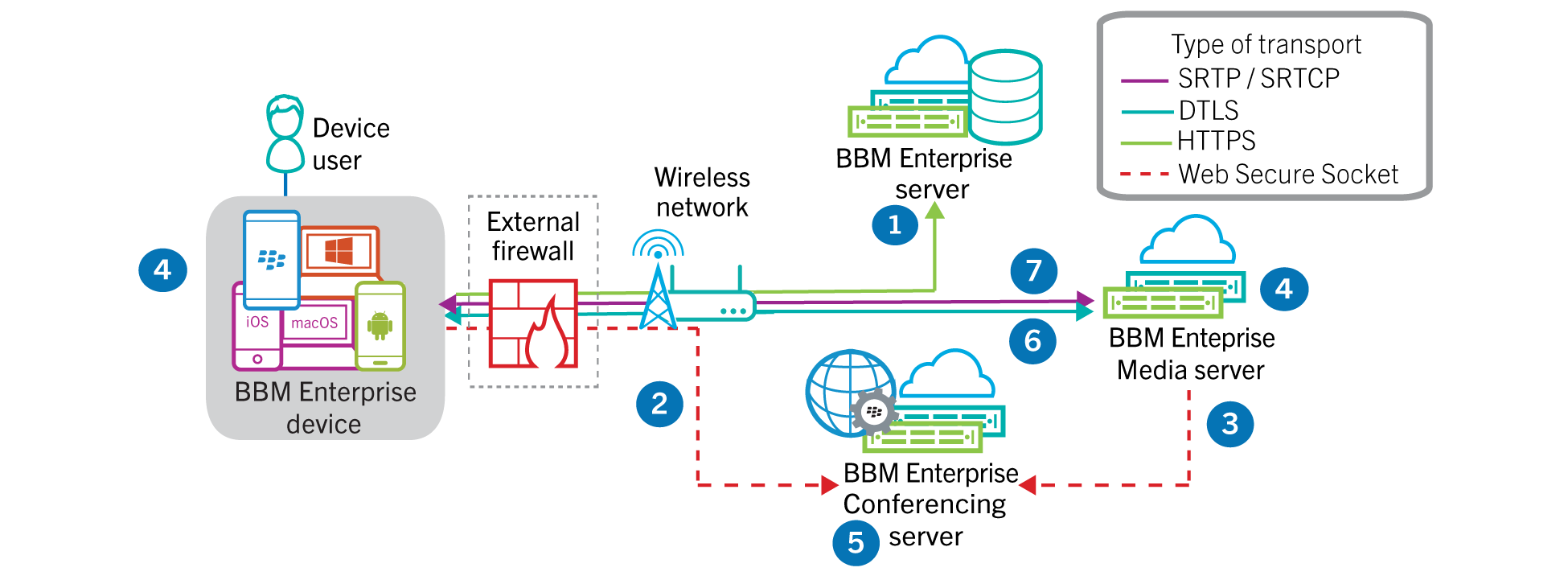
Inventions | Free Full-Text | Determining Information Security Threats for an IoT-Based Energy Internet by Adopting Software Engineering and Risk Management Approaches